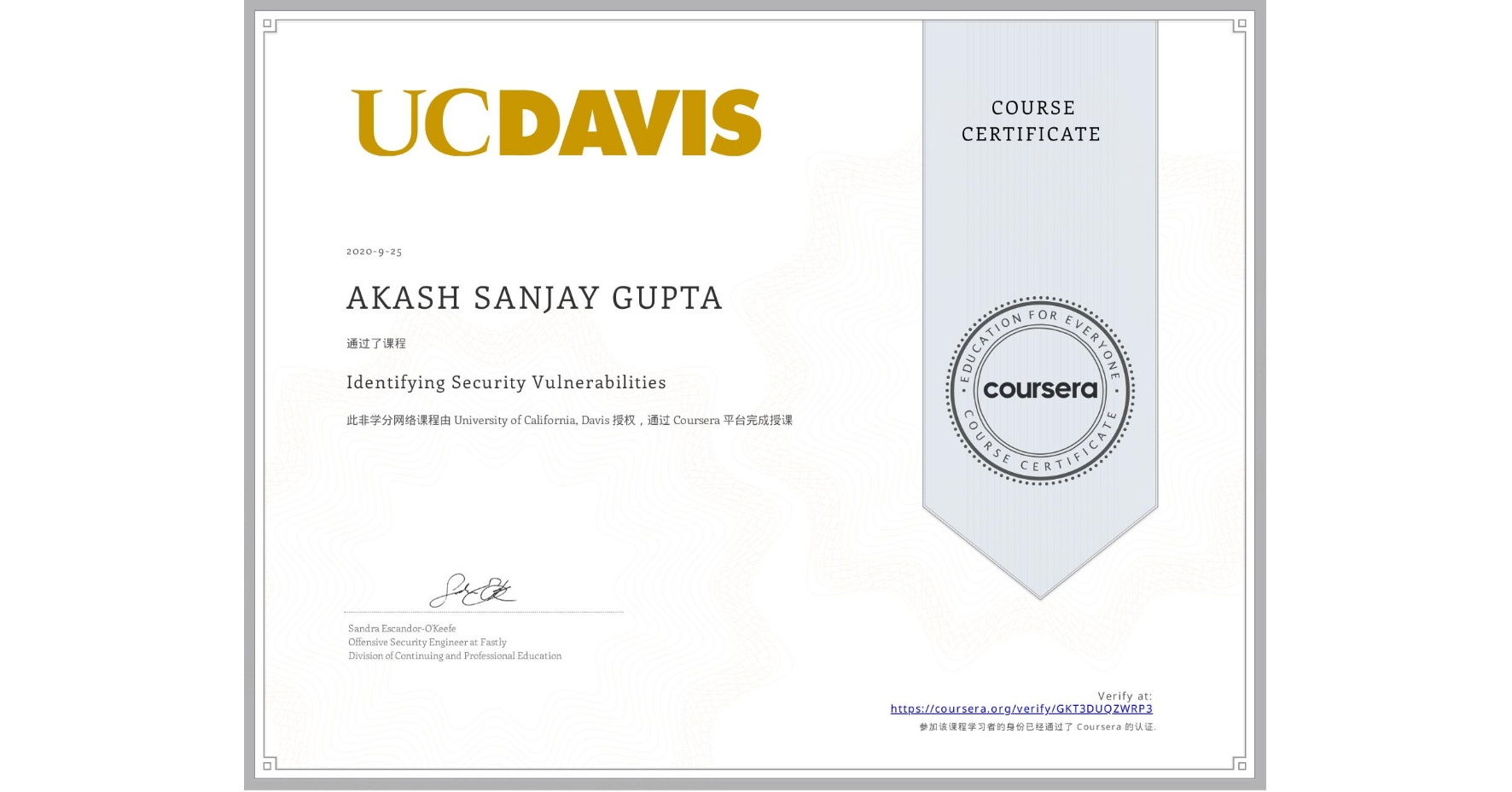
Identifying Security Vulnerabilities
Completed by AKASH SANJAY GUPTA
September 25, 2020
13 hours (approximately)
AKASH SANJAY GUPTA's account is verified. Coursera certifies their successful completion of Identifying Security Vulnerabilities
Skills you will gain
- Category: Data Validation
- Category: Open Web Application Security Project (OWASP)
- Category: Secure Coding
- Category: Cryptography
- Category: Vulnerability Assessments
- Category: Encryption
- Category: Vulnerability Management
- Category: Exploitation techniques
- Category: Security Controls
- Category: Data Security
- Category: Threat Modeling
- Category: Authentications