- Cyber Attacks
- Exploitation techniques
- Network Security
- Threat Detection
- Threat Management
- Cybersecurity
- Computer Security
- Information Systems Security
- Threat Modeling
- Security Engineering
- Encryption
- Distributed Denial-Of-Service (DDoS) Attacks
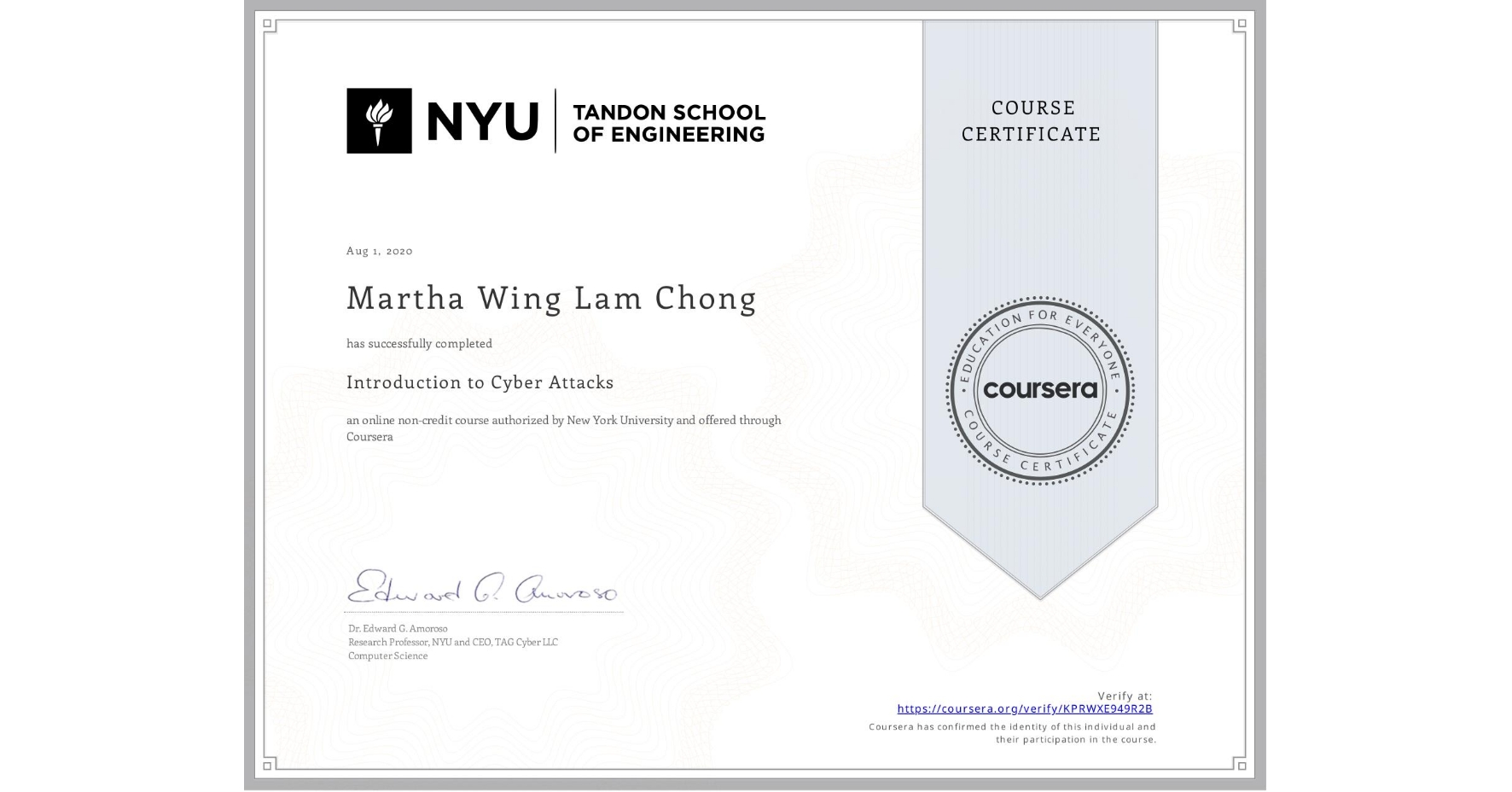
Introduction to Cyber Attacks
Completed by Martha Wing Lam Chong
August 1, 2020
18 hours (approximately)
Martha Wing Lam Chong's account is verified. Coursera certifies their successful completion of Introduction to Cyber Attacks
Skills you will gain