- Docker (Software)
- Vulnerability Assessments
- Authentications
- Vulnerability Management
- Exploit development
- Java Programming
- Secure Coding
- Penetration Testing
- Git (Version Control System)
- Open Web Application Security Project (OWASP)
- Authorization (Computing)
- Java
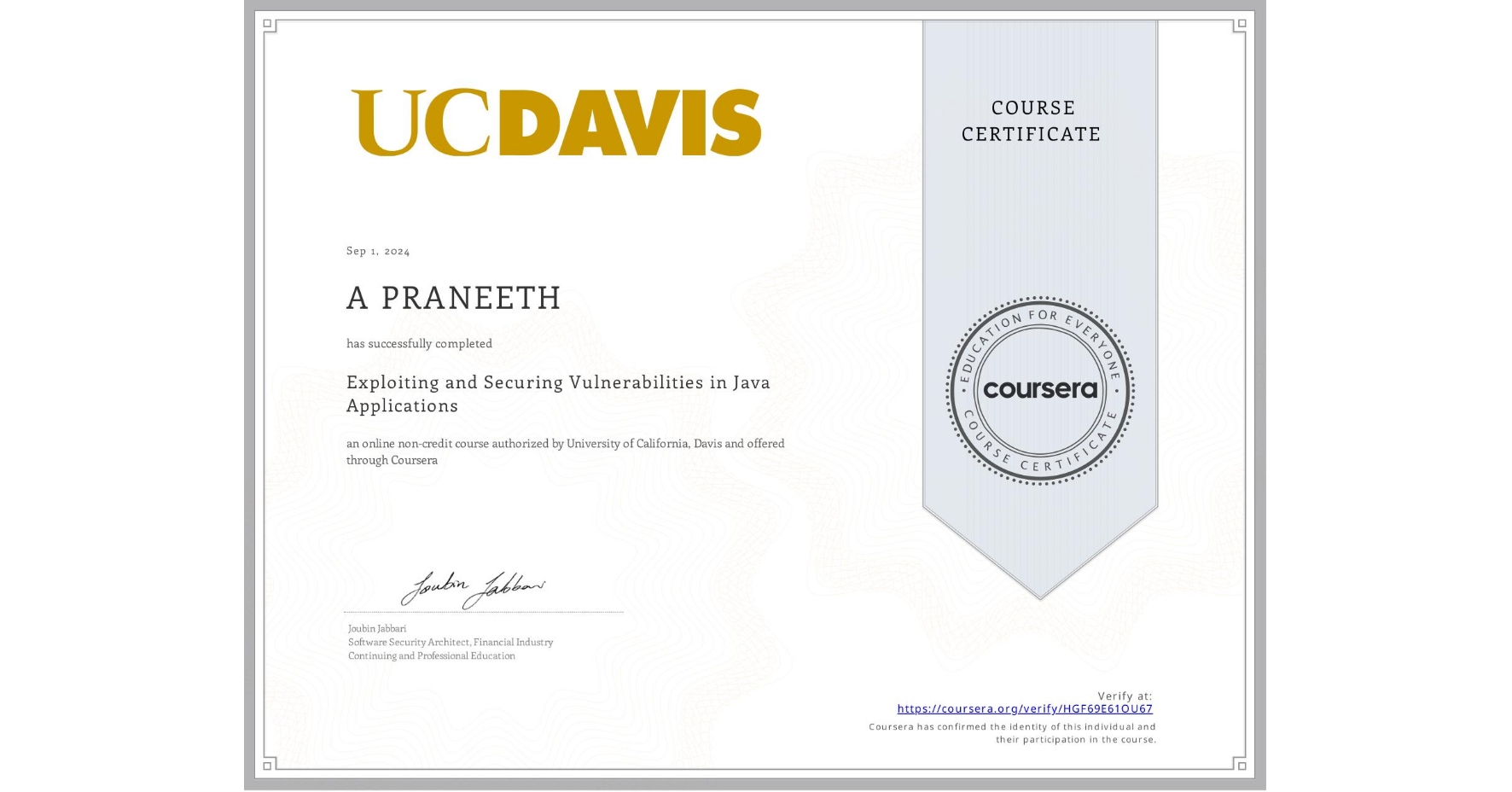
Exploiting and Securing Vulnerabilities in Java Applications
Completed by A PRANEETH
September 1, 2024
23 hours (approximately)
A PRANEETH's account is verified. Coursera certifies their successful completion of Exploiting and Securing Vulnerabilities in Java Applications
What you will learn
Practice protecting against various kinds of cross-site scripting (XSS) attacks.
Form plans to mitigate injection vulnerabilities in your web application.
Create strategies and controls to provide secure authentication.
Examine code to find and patch vulnerable components.
Skills you will gain