- Cryptography
- Test Planning
- MITRE ATT&CK Framework
- Security Testing
- Threat Detection
- Vulnerability Scanning
- Vulnerability Assessments
- Cybersecurity
- Threat Modeling
- Penetration Testing
- Encryption
- Application Security
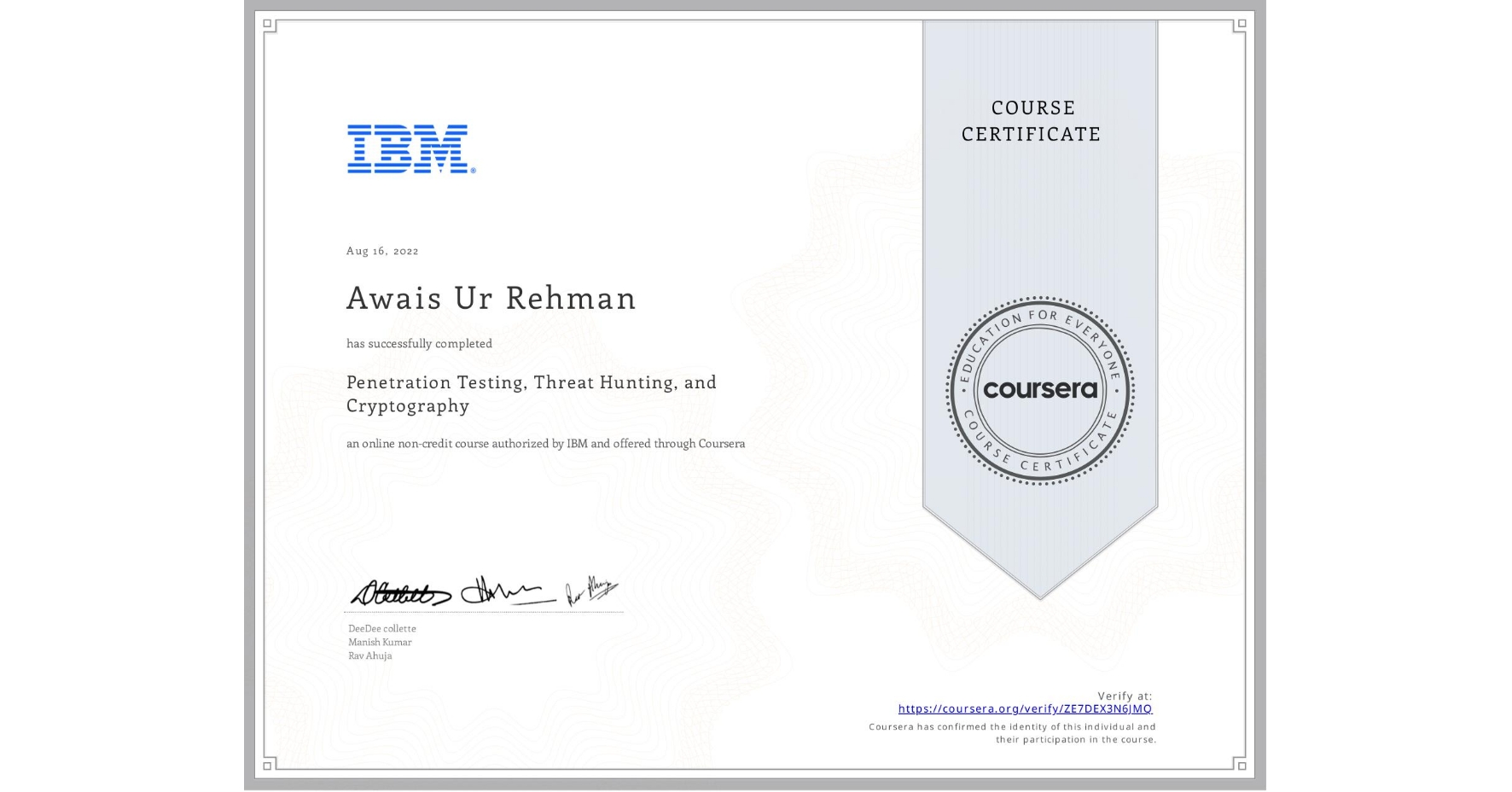
Penetration Testing, Threat Hunting, and Cryptography
Completed by Awais Ur Rehman
August 16, 2022
17 hours (approximately)
Awais Ur Rehman's account is verified. Coursera certifies their successful completion of Penetration Testing, Threat Hunting, and Cryptography
What you will learn
In-demand penetration and threat hunting skills, supported by hands-on practice that employers are looking for on a resume.
Hands-on experience applying the principles of penetration testing using tools, such as OWASP ZAP and SNYK.
How to create penetration testing reports and integrate AI to perform advanced threat hunting and threat intelligence.
Use cryptography and cryptanalysis techniques like encryption and hashing to ensure data integrity and confidentiality.
Skills you will gain